
When I talk with website owners, agency directors, or small business operators, the same concerns come up again and again. They’re worried about their WordPress site getting hacked, clients blaming them for downtime, or waking up to a defaced homepage and no clear way to fix it. Whether you’re managing one WordPress site or dozens in a client portfolio, the underlying goal is the same: keep your site stable, secure, and under your control.
Security doesn’t stop at installing a plugin and calling it a day. A modern WordPress security plan needs to account for multiple levels of protection, from the code inside your site to the server environment hosting it. If you ignore even one of these layers, you leave cracks that are easy to exploit.
This may sound discouraging. Nobody needs more complexity added to their business, but by understanding and applying these principles, it becomes a breeze. We have built security into the DNA of all GillyTech offerings.
The Top Concerns Website Owners Face
- Site defacement or takeover: Hackers replacing your site content or gaining admin privileges
- Malware infections: Injected code that can steal visitor data or redirect traffic
- Slow response to alerts: Security notifications go unnoticed or never arrive in time
- Plugin vulnerabilities: Outdated or poorly built plugins opening up attack vectors
- Brute force attacks: Repeat login attempts that drain server resources and increase exposure
If you’re an agency, tack on a few more layers: cross-site contamination, liability for multiple client properties, and the risk to your reputation if a single compromise spreads across accounts. Security at scale demands structured policies and smart defaults that work consistently across your toolset.
Start With the Full Picture
There is no silver bullet plugin or quick fix. WordPress security in 2026 means you need to think through three key domains:
- Site-Level Protections: WordPress core, themes, plugins, user accounts, and database
- Infrastructure & Services: DNS, CDN, web application firewall, backup workflows
- Server & Hosting Environment: PHP version, web server config, OS-level permissions, monitoring tools
Most attacks don’t break in through the front door. They slide in through an outdated theme, an old abandoned plugin, or a forgotten demo admin account. And even when your WordPress install is clean, that doesn’t mean the server it sits on is secure. A public-facing site involves multiple services all talking to each other. Any weak link is an open invitation.
Why the Layered Approach Matters
If you’re only locking the WordPress admin panel but leaving PHP outdated on the server, you’ve built a false sense of security. Real protection starts with redundancy. Any single layer should catch what the others miss.
For example, consider the combination of:
- A firewall that blocks known bad IPs before they reach WordPress
- A plugin audit policy that removes anything not in active use
- Consistent backups stored off-server with encryption
None of these on their own is enough. Together, they give you coverage across the entire stack. That’s how you stop threats from slipping by unnoticed.
The Cost of Inaction
Let’s be blunt: if you don’t take security seriously, you will get hit—it’s just a matter of time. WordPress is a widely-used platform, and attackers cast a wide net looking for any weakness. Using themes or plugins from sketchy sources, ignoring update alerts, or skipping regular backups puts your entire investment at risk.
If your site brings in leads or revenue, you can’t afford it going down. And if you manage client sites? You’re not just defending software. You’re protecting your client’s brand, their customer trust, and your credibility.
Build Security Into Your Strategy From Day One
Whether you’re spinning up your first install or managing a portfolio of ten, make security a built-in part of your process, not an afterthought. That starts with choosing a host that takes care of performance and patch management intelligently.
Our own managed hosting service, HyperPress, was built around this exact need: consistent speed and airtight security without babysitting dozens of plugins or constantly logging into cPanel. But even with solid hosting, the responsibility doesn’t stop there. You need practices and tools that go beyond the basics.
A secure WordPress site requires a plan that covers all the pieces—site code, infrastructure setup, and server configuration. Skipping any layer puts everything else at risk.
In the next section, we’ll break down exactly how to harden your WordPress site from within WordPress itself—covering the tools, setup steps, and policies that keep your install clean and protected from exploit kits and malware scanners.
Securing the WordPress Site Level
The first and most visible layer of any WordPress security setup starts with the WordPress installation itself. That means hardening the core application against common threats: brute force attacks, plugin exploits, outdated software, and malicious requests that make it through basic filters.
1. Install and Configure WordFence
WordFence remains the most widely deployed security plugin for a reason. It brings a full suite of features to the table: a real-time firewall, malware scanning, login protection, and alerts that actually get your attention.
Start with the free version. It handles core protection tasks well and is easy to configure. Install it from the WordPress plugin repository, then walk through the basic setup wizard. Enable both scanning and firewall protection, and enter your email to receive security alerts.
- Scan Kit: Checks core files, themes, and plugins for changes or anomalies
- IP Lockout: Blocks repeated login failures or known malicious IPs
- Live Traffic View: See what requests are hitting your site in real time
The Pro version is worth considering if you’re handling ecommerce, client-facing portals, or any website that is doing serious traffic. It gives you access to real-time threat intelligence, country blocking (especially useful for limiting attack surface), and premium support features. This level of control is a reasonable upgrade when you’re managing security at scale or want tighter protections by default.
Once WordFence is in place and configured, make it part of your workflow to review its weekly emails and take action on any plugin mismatches or anomalies it finds. Don’t treat the alerts as spam. They’re showing you where cleanup or updates are overdue.
2. Stay Updated: Core, Themes, and Plugins
90% of security issues start with outdated code. Keeping WordPress core, all active themes, and every plugin up to date might sound basic, but it’s the single most effective way to protect against known vulnerabilities.
Your update policy should follow some consistent rules:
- Schedule: Set a calendar reminder once a week to check for updates, or automate them where safe to do so
- Prioritize alerts: Patch anything flagged by WordFence or scanner tools immediately, especially high-risk items
- Remove what you don’t use: If a plugin or theme isn’t active, delete it entirely—not just deactivate it
Outdated software is not just inefficient. It’s a liability. Even if unused plugins seem harmless, they can still offer an attack path if loaded into the environment and not kept secure. This becomes even more important in multisite setups or agencies managing dozens of client installs.
3. Think Twice Before Installing Plugins
It’s tempting to grab the first free plugin that looks like it’ll solve a small problem. But every plugin adds another piece of code that can be exploited. And the worst offenders look legit on the surface, especially if they’re cloned or “nulled” versions of paid tools.
If a plugin isn’t built well or maintained consistently, it’s a weak point.
- Only use plugins from reputable developers and marketplaces with regular updates and public changelogs
- Avoid “nulled” or pirated plugins entirely—many are laced with backdoors or cryptominers
- Limit your plugin count—the more plugins installed, the broader your exposure
The safe default? Use as few plugins as necessary, vet each one before installing, and audit your plugin list quarterly to remove anything no longer essential.
4. Integrate Security into Your Workflow
Security isn’t something you set and forget. It’s a continuous process baked into how you build and maintain the site. At GillyTech, we recommend a model that treats updates and plugin reviews as part of standard maintenance—not optional tasks saved for downtime.
For owners on our HyperPress hosting platform, nearly all of this is handled automatically behind the scenes and you will be 100% covered. But even then, making sure you aren’t using any abandonware plugins or taking unreasonable risks is still your responsibility.
This is where too many site owners fail—not at configuring tools, but at committing to consistent upkeep.
Start with WordFence. Keep your site updated. Avoid sketchy plugins. This is the baseline for any serious WordPress site in 2025. If your business depends on that site staying online, these aren’t “nice to have” steps. They’re required.
Once you’ve locked things down at the WordPress level, the next big leap in protection comes from infrastructure-level tools—things like CDNs and firewalls that stop bad traffic before it ever touches your CMS. We’ll cover that next.
Infrastructure Protection Beyond WordPress
Once your WordPress installation is hardened at the site level, the next step is strengthening the infrastructure that supports it. This includes how content is delivered, how bad traffic is filtered before it ever reaches your site, and how your hosting stack keeps malicious behavior at bay.
What a CDN Really Does
A Content Delivery Network (CDN) is more than just a speed booster. While it helps distribute content faster by caching static assets across servers around the world, it also plays a critical role in resilience and protection.
A properly configured CDN absorbs traffic spikes, distributes bandwidth load, and filters requests geographically. This means your origin server doesn’t get overwhelmed by bots or DDoS attempts. More importantly, with the right provider, you get performance and security benefits together.
Why QUIC.cloud is the Smart Pick for LiteSpeed Users
If you’re using a LiteSpeed web server (often bundled with high-performance WordPress hosting), QUIC.cloud is the most compatible and feature-rich CDN available. Unlike general-purpose CDNs, it integrates tightly with your web server’s native cache system and supports dynamic content delivery—not just static files.
Benefits of using QUIC.cloud with LiteSpeed:
- Full-page caching that respects WordPress rules and dynamic behavior
- Seamless integration with the LiteSpeed Cache plugin
- Geo-blocking and DDoS protection mechanisms built in
This setup gives you granular control. You can serve publicly cached content extremely fast while keeping login sessions, carts, and forms protected and dynamic. For LiteSpeed-based hosting environments—like those we deploy at GillyTech—QUIC.cloud is a logical fit.
If you’re using Apache or NGINX, there are other CDN options worth considering, but don’t automatically reach for the standard names bundled into budget hosting plans. Some of the more popular solutions have inconsistent uptime and support problems. We’ve covered those risks here in more detail.
What a WAF Does and Why You Need One
A Web Application Firewall (WAF) is the gatekeeper between the public internet and your website. It filters all incoming HTTP traffic and decides what to let through based on rules, behavior patterns, and threat signatures. This is your first wall of defense against injection attacks, brute force attempts, bots, and malformed requests.
Without a WAF, every visitor—including those with bad intentions—gets to knock at your front door directly.
There are two ways to deploy a WAF for WordPress:
- Application-level WAFs like WordFence (already running on your WordPress install) inspect traffic once it’s touched PHP. Useful but reactive.
- Edge-based WAFs that screen requests before they hit your server. These are cloud-layer protections built into services like QUIC.cloud or premium hosting panels.
If you can only pick one, choose an edge-based WAF. These solutions absorb threats upstream, conserving server resources and minimizing exposure inside WordPress itself. It’s a proactive rather than reactive form of defense.
Best Practices for Setting Up Infrastructure-Level Protection
Your infrastructure security checklist can follow this framework:
- Use a CDN that integrates with your server stack (QUIC.cloud for LiteSpeed, or [insert preferred provider] for Apache/NGINX)
- Enable the WAF feature within that CDN or choose a cloud WAF provider that supports edge-level protection
- Apply geo-fencing and rate-limiting rules to cut off entire regions that don’t need access to your site
- Monitor and tune your threat log weekly to update access control rules based on failed logins or spam patterns
In hosted configurations, this upstream protection can often be enabled with a switch inside your hosting control panel. But don’t stop there. Take time to configure the blocking rules smartly. Default settings are a starting point, not a strategy.
Infrastructure-level protection is what shields your WordPress install from overload, exploits, and zero-day attacks targeting popular plugins or login portals.
Closing the Gaps WordPress Alone Can’t See
That’s what sets infrastructure protections apart from plugins—they don’t just react, they prevent.
Pair a CDN with a native WAF, and you create a buffer zone between your live website and the open internet. This is how you buy time, control your exposure, and keep performance high while keeping threats out.
Backup Strategies That Ensure Recovery
You can lock down your WordPress install and firewall your infrastructure, but if you don’t have clean, offsite backups, you’re gambling with uptime. A single corrupted file, ransomware attack, or unexpected server failure can wipe out weeks—or years—of work. Recovery planning isn’t optional anymore. It’s a core part of securing your site.
Why Backups Are a Security Tool
People often think of backups as a safety net for mistakes or someone accidentally deleting a file. But in security practice, backups are your last line of defense when everything else fails—when malware destroys key files, when your host suffers a catastrophic issue, or when a rogue plugin update breaks your entire install.
A complete, recent, and externally stored backup can mean the difference between a quick restore and days of downtime.
This is especially important if you run an ecommerce store, lead generation site, or manage multiple client properties. Recovery time affects revenue, reputation, and client relationships in measurable ways.
Use WPvivid for Scheduled Backups
I’ve used a lot of backup plugins over the years, and WPvivid continues to be one of the easiest and most reliable for scheduled WordPress backups. It handles everything a production site requires:
- Full-site backups: Files, databases, and even staging environments if configured
- Incremental backups: Only updated files are backed up after the first full copy, reducing storage and processing time
- Flexible scheduling: Daily, weekly, or custom cycles based on your content update habits
- Automatic offsite transfer: Supports several external storage destinations, including SFTP, Google Drive, Amazon S3, and Backblaze B2
Set it up once inside your WordPress dashboard, verify email notifications, and make sure the test restore works before you assume you’re covered. A backup that fails to restore when needed is no better than no backup at all.
Store Backups Offsite (And Encrypt Them)
It’s not enough to store backups on the same server or hosting account as your live site. If your server gets compromised or ransomware hits your host, those local backups are either encrypted or deleted along with everything else.
The best practice is simple:
- Store each backup in a physically separate location from your live site
- Use encryption to protect the data before or during transfer
- Automate the movement and purging of old backups to avoid bloating your storage quota
Backblaze B2 is a strong choice here. It’s cost-effective, supports encrypted uploads, and integrates cleanly with WPvivid. Once connected, you can configure automatic uploads and set rotation policies to retain the latest [insert count] versions while deleting anything older.
One important setting to utilize is the minimum time limit for keeping files. Think of it as a timed lock for deleting files and there is a good reason to use it. Particularly nasty malware will actually seek out backups on external services and attempt to delete any backups through the plugin interface. This is a great defense against this type of attack and ensure you can access your backups after an attack of any kind.
Don’t copy files manually. That process doesn’t scale and it’s too easy to forget. Use automation and alerts to ensure backups are generated and uploaded without needing hands-on work each week.
Backup Strategy Framework
If you’re not sure where to start, use this simple structure to guide your policy:
- Daily Incremental: Small updates backed up every 24 hours
- Weekly Full: Entire site backed up once a week, stored offsite with encryption
- 90-Day Retention: Keep at least three full months of restore points
- External Storage: Use something like Backblaze B2 rather than local folders or shared hosting space
- Test Restores: Every quarter, restore to a staging site to confirm the process works
If you manage client sites or run an agency setup, develop shared policies across all installs. Keep configuration templates, enforce naming conventions for backups, and use separate storage containers per client to avoid confusion or cross-contamination.
You can also combine this with uptime monitoring (covered later in this guide) so that if a site goes down unexpectedly, you already have the recovery tools in place to act within minutes, not days.
What Not to Do With Backups
There are a few common mistakes that I see over and over:
- Relying on your host’s internal backup system only, especially on shared hosting. These are often incomplete, slow to restore, and not always freely accessible.
- Backing up to the same account as live WordPress files, which defeats the purpose of isolation during an attack
- Disabling encryption, which leaves your database or user passwords exposed in storage
- Never testing a restore process, which means you’re flying blind when something actually breaks
Fix those and you’re already ahead of most WordPress site owners.
Security Without Recovery Is a False Sense of Safety
If you’re doing everything else right—firewalls, updates, plugin reviews—but skipping backups, you’re assuming nothing will go wrong. That’s not realistic. Things break. Updates fail. Bad actors get through. Without a recovery path, every small error turns into a major threat.
Set up WPvivid, send backups to a secure offsite location like Backblaze B2, and double-check that encryption is active. That’s it. No excuses, no skipped steps.
For more structured hosting guidance, you might want to review our WordPress hosting strategy guide for 2026. Even the best server can’t help you if your backups aren’t configured properly.
Make recovery a standard part of your WordPress workflow—not something you think about after disaster hits.
Server Hardening and Configuration
Even with WordPress, your site code isn’t the full story. The security of the underlying web server and its configuration plays a major role in whether your website stays protected—or gets exploited. I’ve helped hundreds of site owners clean up hacked installs that never would’ve happened if the server had been properly hardened from the start.
Follow CIS Benchmarks for Web Server Security
The CIS Benchmarks are your blueprint for industry-recognized server security. These are vendor-neutral guidelines developed by security professionals for securing infrastructure components like Apache, NGINX, MySQL, and other services commonly used in hosting WordPress.
They break down hardening tasks into actionable categories:
- Basic OS configuration and user account controls
- Service-level permissions and secure listening ports
- Firewall and SSH access policies
- File system lockdowns (no-execute, read-only)
- Logging, auditing, and intrusion detection flags
You don’t need to implement every rule. But if your server fails major control points like unrestricted SSH access or public write permissions on web directories, you’re walking on thin ice.
If you’re on a VPS or dedicated server, read through the CIS checklist for your stack and start applying one item at a time. For managed hosting, check with your provider to confirm which benchmarks they’ve implemented and where you still need to add coverage.
Run a Supported PHP Version
This is one of the most overlooked layers of basic security. A significant number of WordPress breaches happen on sites using out-of-date PHP versions that are no longer getting security patches. These unpatched versions are wide open to known exploits that attackers regularly scan for.
Check what PHP version your server is running today. Then cross-reference it here: https://www.php.net/supported-versions.php
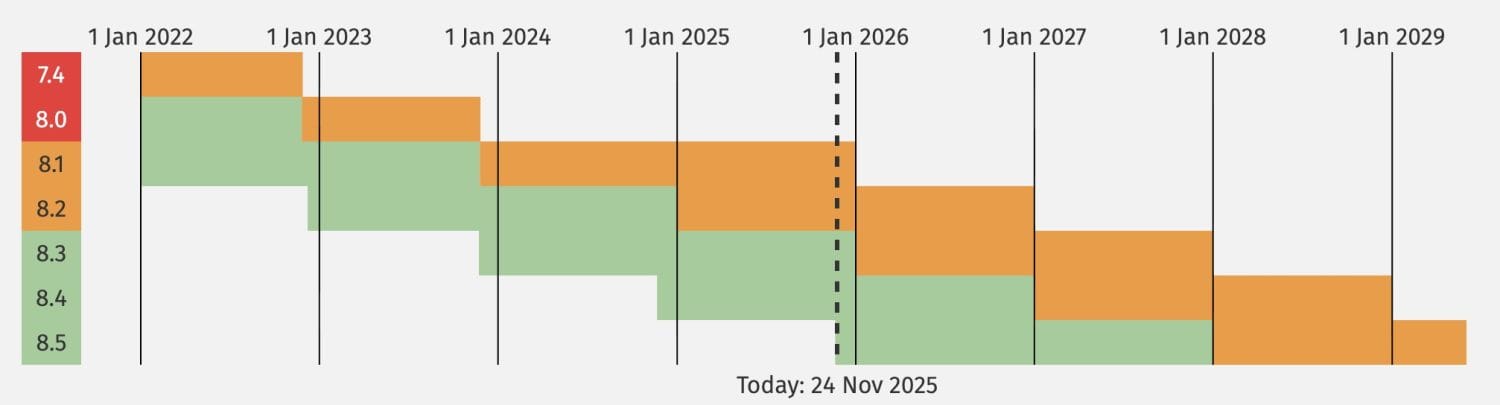
If you’re running anything that’s no longer receiving active support or security fixes, upgrade immediately. This isn’t optional. A modern WordPress install should be running a stable, supported PHP version with all patches applied regularly as part of your overall update policy.
If your hosting provider doesn’t support current PHP versions, that’s a sign your environment hasn’t been maintained properly. That’s a major red flag. You either need to switch hosts or move to a better-managed infrastructure setup that allows this kind of control.
Keep Server Software Updated and Patched
Running the latest WordPress release is good. But it won’t matter if your server’s operating system, web server, SSH stack, database engine, or control panel is outdated or exposed. Updates exist for a reason—and software that faces the public internet needs to get those updates routinely.
Here’s a basic framework to follow:
- Apply OS-level package updates at least monthly to catch kernel upgrades and service patches
- Monitor change logs for Apache, NGINX, MySQL, and PHP and keep each component within its supported lifecycle
- Watch for control panel updates (like cPanel, DirectAdmin, or Plesk) and install security patches as soon as they’re available
Missed patches are the soft underbelly of most compromised hosting environments. Set reboots and maintenance windows if you need to, but don’t put this off. Keeping packages up-to-date is cheaper than recovering from a breach.
Monitor Server Health Proactively
Hardening only works when it’s enforced—and enforcement means monitoring. Symptoms like increased CPU usage, failed login attempts, or unexplained processes are often missed until the server slows to a crawl or the site goes offline.
At a minimum, configure alerts for:
- Excessive load averages or unexpected memory usage
- Repeated SSH login failures from unknown IPs
- Disk space running low in /var or /home partitions
For more advanced environments, I recommend setting up centralized monitoring with tools like Zabbix. It allows you to track metrics across multiple servers, set up alert logic, and visualize trends over time. If you’re not ready for that level of system orchestration, even basic system monitoring tools installed via your panel (like Netdata or CSF/LFD) provide meaningful visibility.
Agencies managing client sites should standardize these tools across installs. Know what’s normal. Track what’s changing. And don’t wait until a client calls you to report downtime.
If you want to go further on performance alongside your security posture, also look into our performance strategies for WordPress hosting environments. Security and speed are tied closely at the configuration level.
Hardening Isn’t Optional When You Own the Stack
If you run your WordPress site on a VPS or dedicated server, none of this is your host’s responsibility. This is your job. Skipping the hardening phase invites attack chains that automated bots exploit 24/7. No firewall or WordPress plugin can protect a misconfigured web server.
Use CIS Benchmarks. Run supported PHP. Apply your updates. Monitor everything.
A secure site depends on the foundation it’s built on. And in WordPress hosting, that foundation starts with the server.
Account Isolation Best Practices
If you’re using shared hosting or a cPanel-based environment to run multiple WordPress sites, you need to revisit your account layout. One of the most overlooked threats in these setups is cross-site contamination—where a compromise in one website spreads to others living on the same account. It happens more often than people think, especially when all sites share a single file system with read/write access.
The fix is simple: isolate each WordPress site into its own hosting account.
This is not a performance trick or a convenience suggestion. It’s a foundational security measure that uses separation to contain risk. Compartmentalization isn’t just for enterprise firewalls. It’s a best practice for anyone hosting more than one WordPress install under the same roof, particularly in shared environments.
Why One Site Per Account Matters
In a cPanel or DirectAdmin environment, it’s easy to spin up multiple domains inside a single account. But from a file system perspective, they’re all living together—and typically under the same PHP user and group. If a vulnerability in one plugin allows uploads or code execution, that attacker doesn’t just control the affected site. They now have access to everything else in that account folder.
This means a single infected site could:
- Modify or delete other site files
- Access database credentials if file permissions are loose
- Install malware across unrelated domains hosted on the same account
If you’re hosting client sites, this turns one careless plugin decision into a multi-site breach.
Keeping each site on a separate account puts a hard boundary between them. Infection in one site stays isolated. Cleanup is faster. Liability is lower. And most importantly, your risk exposure doesn’t multiply linearly with every new project you launch.
How to Structure Hosting Accounts for Isolation
In practical terms, here’s how to implement account isolation depending on your environment:
- For cPanel/DirectAdmin users: Create a separate cPanel or DirectAdmin user for each WordPress site. Don’t stack multiple domains inside one account.
- For VPS or dedicated servers: Use a dedicated system user (and optionally, a chroot or container) per WordPress site. Assign file ownership and web root permissions carefully.
- For agencies or resellers: Use hosting plans that provide account-level separation with dedicated PHP pools. This prevents resource bleed and keeps logins, file systems, and services fully independent.
If your host limits you to one user account and expects you to run all your WordPress sites side-by-side, you’re cornered into a bad security model. That’s when it’s worth looking at alternatives more tuned for multi-site management. You can find recommendations in our hosting strategy breakdown.
Backup and Recovery Within Isolated Accounts
Account isolation also simplifies recovery and backup management. Each WordPress installation can have:
- Its own scheduled backup cadence
- Individual encryption and remote storage configuration
- Separate log files and access reports for threat analysis
When something breaks, you restore only the affected site. You’re not sifting through shared access logs or hoping your backup tool knows which database belongs to which project. Everything is compartmentalized—by design.
Watch for Internal Plugin Dependencies
A common mistake when migrating to isolated environments is assuming that all interconnected WordPress sites will still “talk” to each other the same way. If you’re using shared resources, such as a common plugin stack or cross-domain AJAX calls, plan for those connections to require secure configuration moving forward.
Don’t bind isolation and fail it with lazy integration. Make sure each site has its own assets, resources, and credentials. Shared plugin folders or centralized wp-content sections defeat the entire purpose.
Isolation Adds Predictability for Monitoring
One overlooked benefit of architecture-level separation is better specificity in monitoring. Attack spikes, CPU load, file changes, and disk usage are easier to pin down when each WordPress site lives in its own sandbox. You don’t get ambiguous alerts saying “something” is wrong—you narrow it down to which site, account, or user is generating the issue instantly.
If you’re using monitoring platforms like Zabbix (helps at scale) or WPMain (good for agencies), spreading your WordPress instances across individual accounts will align directly with how those tools group, target, and trigger alerts.
Bottom Line: Don’t Bundle Projects Together
It’s tempting to take the fast route and tuck all your WordPress installs into one account to save a few dollars or steps. But cutting corners here compromises all your other security efforts. Think sandboxed. Think separate. And don’t co-locate unrelated projects on the same user, panel login, or file system.
Account-level separation gives you containment. Containment gives you control.
If you’re unsure how to migrate into isolated accounts without breaking themes, plugins, or email deliverability workflows, we consult directly on these types of transitions. Drop us a note on the contact page, and we’ll walk you through the architecture that makes sense for your stack.
Spam and Attack Mitigation Techniques
Even after you’ve hardened your WordPress install and protected the server infrastructure, one area gets overlooked too often: stopping spam and automated attacks from clogging your site’s entry points. Bots will hit every form they can find. Login portals, contact forms, comment sections—all of them are exploited for brute force attempts and spam injection unless you put controls in place.
Monitor Spam and Attack Rates Proactively
You can’t improve what you don’t measure. Start by paying attention to the following surface-level indicators:
- Unusual spikes in failed login attempts or invalid username/password combinations
- Form submissions with duplicated content, SEO links, or gibberish
- Security scanner traffic from known bot networks trying to probe for plugin vulnerabilities
If you’re using WordFence, check the “Live Traffic” tab regularly. It shows you what IP addresses are attempting logins, posting comments, or hammering specific URLs. Repeated hits on your /wp-login.php or XML-RPC endpoints should flag an elevated threat posture.
Outside WordFence, some hosts log access attempts directly in server logs. Review those files weekly or use tools that aggregate and flag anomalies. If you’re an agency managing client properties, this type of logging should be standardized and centralized across your installs.
Add Friction with hCaptcha to Block Bots
Spam bots aren’t filling out contact forms manually. They’re submitting forms via scripts that detect open fields and blindly pipe in promotional junk, malware links, or phishing payloads. You need a form-access gate that’s worth more than a checkbox.
hCaptcha is a free, privacy-respecting solution that’s stronger at detection than most default options. It works by presenting challenge-response tests that are nearly impossible for automated bots to complete but fast for humans. Unlike alternatives that focus on user tracking, hCaptcha focuses on behavioral patterns and static image logic to distinguish users from junk traffic.
Integration is straightforward for the major WordPress form builders:
- Gravity Forms: Offers native hCaptcha integration with toggle settings in each form’s anti-spam settings
- WPForms: Add hCaptcha alongside or in place of reCAPTCHA directly from the form editor
- Contact Form 7: Use the hCaptcha plugin to register your site keys and drop shortcodes inside each form template
Once set up, test the full submission flow: Desktop and mobile users should pass easily. Scripts will bounce. This reduces your email load, keeps your inbox clean, and prevents malicious payloads from even entering your database or triggering alert fatigue.
Checklist for Hardened Form Submissions
Whether you’re using one form plugin or several across a site, your anti-spam policy should follow a few simple principles:
- Use hCaptcha on all public-facing forms including contact, comment, registration, and newsletter entries
- Limit POST frequency by IP using server rules or plugin-based rate limiting
- Disable or rename exposed endpoints such as /wp-login.php and /xmlrpc.php if not actively used
- Filter known spam keywords using plugin-based filters or SMTP-level rules on outbound mail
Getting even half of this in place will dramatically cut down on bogus leads and bot activity. If you’re running a larger site or managing client installs, go a step further and centralize submission logs so that unusual trends stand out early during your review cycles.
Form Traffic is a Gate—Not Just a Feature
It’s easy to treat contact forms as passive features on your site. But every field you publish, every button that triggers a POST request, is a gateway attackers can abuse.
The fix isn’t removing your forms. It’s reinforcing the entries with intelligent friction that stops bots but stays friendly for users. hCaptcha does this well without the invasive practices some older CAPTCHA systems relied on.
Lock down your forms, watch the traffic, and reset your tolerance for spam to zero.
If you need help tuning your tools or identifying blind spots in your attack surface, book a quick call with our team. Protecting your site isn’t about guesswork—it’s about control and consistency.
Security Monitoring and Alert Systems
You can’t fix what you don’t know is broken. Most compromises aren’t discovered because someone spots them right away—they’re found after analytics tank, users complain, or spam gets delivered from your domain. Monitoring and alerts are how you stay ahead of damage, not clean it up after the fact.
Enable WordPress Security Alerts
Start by turning on email notifications inside your WordPress security tools. If you’re using WordFence (which we’ve already walked through), it can send real-time updates for failed logins, file changes, or blocked IP hits. Go into the plugin settings and make sure alert thresholds are configured, emails are correct, and volume levels aren’t muted or overly aggressive.
If you’re not reviewing security emails regularly, you’re flying blind. Set a rule in your email client to route alerts into a folder you check once a day. Mark any that contain plugin updates, admin logins from new locations, or IP blocks with high threat scores for monthly review.
If your email service supports it, enforce DKIM/SPF headers on outgoing alerts so they don’t land in spam. Also check that alerts include accurate timestamps and IPs—useful later when correlating activity across firewall logs or external monitors.
Monitor Site Uptime with External Tools
No matter how locked-down your site is, availability still matters. Even a perfectly secure WordPress install isn’t useful if it’s offline, slow to respond, or returning bad responses. That’s where uptime monitoring comes in.
External monitors simulate visitor sessions from outside your hosting network. They ping your site from various locations and alert you if it fails to load, returns a 500 error, or begins timing out. This gives you outside-in visibility into performance and availability, not just backend diagnostics.
When configuring an external monitor, use these best practices:
- Set intervals to every 5 minutes or less—longer delays lead to late detection
- Use multiple test locations to confirm regional reliability issues
- Test both the homepage and critical endpoints like forms, cart pages, or login areas
You don’t have to start with enterprise tools. There are plenty of options that offer alerts by email or webhook. Route those alerts to your ops workflow, ticket system, or Slack for real-time event logging.
Never wait until a customer reports downtime. The goal is knowing about the issue before anyone else does.
Step Up to Zabbix for Advanced Monitoring
If you’re managing multiple WordPress installs or running on a VPS or dedicated server, basic uptime checks aren’t enough. This is where Zabbix comes in. It’s a full-featured monitoring framework that tracks server-level health, service metrics, and custom WordPress behaviors across multiple environments.
Use Zabbix to monitor and alert on:
- Disk usage across partitions like /var, /tmp, and /home
- Nginx/Apache service restarts or failures
- MySQL query time spikes or process saturation
- Backup script success/failure logs
- Firewall activity, failed SSH logins, and port status
Zabbix runs as a central server with agents on each monitored node. You control thresholds, alert pathways, and visualization dashboards. This isn’t just a “set it and forget it” tool—it’s an architecture decision that gives you root-level intelligence on how your hosting environment performs under load, attack, or software failure.
If you’re not ready for Zabbix, consider hosted infrastructure options with built-in monitoring dashboards that approximate similar features. But if you’re serious about uptime across a fleet of sites, nothing beats the flexibility and depth Zabbix provides.
Leverage WPMain for Agency Monitoring
Running multiple client sites isn’t just about making updates—it’s about knowing whether anything changed when it wasn’t supposed to. WPMain helps agencies tie together multi-site maintenance, plugin audits, and update events into one console built for scale.
WPMain centralizes:
- Plugin and theme update status across all managed WordPress installs
- Security alerts pushed from WordFence or similar plugins
- Scheduled client reports on uptime, change logs, and backups
Consider WPMain your single dashboard for the health and risk posture of all your active projects. If a plugin gets pulled from the repository, a theme license expires, or Google starts detecting phishing content—this is where you see it first.
For teams with SLA-driven client relationships, it prevents reactive scrambling by giving you the facts before your inbox fills with complaints. Fewer surprises. Better forward planning. More consistency across accounts.
Monitoring Is the Final Layer of Control
You can’t protect a site you’re not watching. Monitoring closes the loop between prevention and action. Tools like WordFence notifications, uptime checks, Zabbix agents, and dashboard aggregators all work together to make sure nothing goes unnoticed—and nothing stays broken for long.
Set them up. Tune them smartly. And review them weekly—not just when something blows up.
If you’re reviewing your broader hosting configuration or looking to standardize monitoring practices across teams, start by benchmarking which alerts matter most to your business model. For more structured advice on managing multi-site hosting, see our guide on why specialized web consulting matters in 2025.
Future Security Trends for WordPress in 2026
The way we authenticate and protect access to WordPress sites is evolving fast. In 2026, the focus no longer rests solely on strong passwords—or even plugins that limit login attempts. Today’s security posture needs to account for password management, multi-factor authentication, and mobile-level protections that go beyond the WordPress dashboard.
Use a Password Manager, Not Your Memory
If you’re still trying to remember multiple complex passwords, you’re doing it wrong. Long gone are the days when memorizing or reusing credentials was a sustainable security approach. The proper standard today is using a password manager—a trusted tool that acts as a secure, encrypted vault for all your logins.
A password manager lets you:
- Create complex, unique passwords for every WordPress site, user account, and admin system
- Fill in credentials securely without writing anything down or exposing them in plain text
- Store critical access keys, hosting credentials, and recovery codes in one encrypted location
Think of it as a centralized, encrypted keychain. It replaces the sticky notes, browser autofill risks, and reused passwords that attackers rely on to gain access. If you can’t remember your admin password, that’s a good sign—you shouldn’t have to. Let the manager handle storage. You just focus on strong master access.
One Strong Password + Password Manager is the New Standard
The argument used to be: create long, random passwords and never use the same one twice. That’s still true, but in real-world practice, it only works if you’re using a password manager to do the heavy lifting. The model we recommend for all WordPress site owners is simple:
- Use one strong master password to secure your password manager
- Let the manager generate unique passwords for every admin user, cPanel login, database access point, and web service
- Store emergency access codes (for 2FA and recovery scenarios) inside encrypted notes or secure vault storage
Do not rely solely on browser password saving tools, especially if you’re sharing devices or managing client credentials. A proper password manager provides greater control, better encryption, and secure sharing workflows—ideal for agency environments with rotating team members or delegated access responsibilities.
Move from SMS to App-Based Two-Factor Authentication
Two-factor authentication (2FA) is no longer optional when securing access to websites. But the method you use can make a big difference in how secure your system really is. SMS-based 2FA—where a code gets texted to your phone—is now considered weak by modern standards. It’s easy to intercept, spoof, or bypass through SIM-related attacks.
Switch to authenticator apps such as:
- Google Authenticator
- Authy
- Duo Mobile
These apps generate time-based one-time codes (TOTP) on your device that aren’t tied to your phone number. They can’t be intercepted or redirected by criminals targeting your telecom carrier. Most modern WordPress security plugins, client portals, and hosting panels support app-based 2FA directly. If your tools only support SMS, it’s time to upgrade.
Enable a SIM PIN Lock to Stop SIM Swapping
SIM swapping is the silent killer for a lot of hacked accounts in recent years. It works like this: someone pretends to be you, calls your cell provider, and convinces them to transfer your phone number to a new SIM card. Now they receive all your calls and texts—including security codes tied to your logins.
Once attackers control your phone number, they can trigger password resets, fake verification processes, and break into connected services in minutes. And worse, you might not notice until your accounts are already compromised.
The fix? Request a SIM PIN lock from your mobile carrier. It’s a separate 4-to-8 digit code that’s required for any support rep to make changes to your account or port your number. Carriers in the US offer this—sometimes by request, sometimes buried in online account settings. Set it, store it securely, and confirm that your number can’t be moved without it.
Your 2026 WordPress Login Security Framework
If you want to align with this year’s best practices, use this as a checklist for securing all login points tied to your WordPress stack:
- Adopt a dedicated password manager to store and generate unique credentials for each tool, user, and environment
- Create one strong master password (avoid dictionary words, include symbols and length) and never reuse it
- Enable 2FA using an authenticator app instead of SMS for all admin-level accounts
- Apply a SIM PIN lock with your mobile carrier to prevent number hijacking
- Set recovery codes and backup access points now to avoid lockouts later
If you’re running multiple sites or managing clients, roll this framework out across all installs, admin accounts, and panel logins. Don’t wait for a compromise to spark policy upgrades. Implement these controls now, and verify adoption monthly as part of your maintenance cycle.
Smart credential management is part of a modern WordPress security plan. If you’ve already taken steps with WordFence, CDN hardening, and backups, this is the last piece that truly locks the front door.
Your login system isn’t secure if it’s easy to forget—and easy to guess.
Get a password manager in place. Use 2FA the right way. And stop letting SMS stand between your site and a breach.
Conclusion and Next Steps
Securing a WordPress website in 2025 isn’t one decision—it’s a series of well-executed steps that work together. There’s no single plugin, firewall, or backup tool that solves everything. Security comes from architecture, consistency, and layering protection points across every level of your stack.
Let’s recap the essentials of a modern WordPress security strategy:
- At the site level: Use WordFence (free or Pro), keep WordPress core, themes, and plugins updated, and only install trustworthy plugins.
- At the infrastructure layer: Protect your site with a reliable CDN—preferably QUIC.cloud if you’re using LiteSpeed—and layer an edge-based Web Application Firewall in front of incoming traffic.
- For backups: Use WPvivid with automated scheduling, encrypt your backups, and send them to an offsite location like Backblaze B2.
- On the server: Harden your configuration using CIS Benchmarks, run a supported PHP version, and patch all software routinely.
- In your account structure: Isolate each WordPress install into its own hosting account to prevent cross-site contamination.
- To reduce spam and attacks: Add hCaptcha to all forms and monitor traffic for brute force attempts or bot behavior.
- For visibility: Enable alerts through your WordPress security plugin, use external monitoring tools for uptime, and central platforms like Zabbix or WPMain for more advanced tracking.
- From a user-practice angle: Stop relying on memory for credentials. Use a password manager, activate 2FA via apps (not SMS), and lock down your SIM to block port-out fraud.
When every layer is doing its job, no single failure results in a catastrophe. That’s the benefit of investing in depth—not just surface-level fixes or reactionary tools.
If you’re a solo site owner, work through each level methodically. Don’t rush it. A single improvement each week gets you to a fully secured deployment within a month. If you’re managing a dozen or more installs for clients, establish policy templates, shared tools, and review schedules. Don’t rebuild protocols every time. Standardize where it counts.
Security isn’t just about today’s risks—it’s about being ready for tomorrow. A breach will cost you far more in time and reputation than doing things the right way from the start. And if you’re tired of managing all of this alone, take a look at our latest posts or connect with us for a review of your hosting strategy and site setup.
You can’t outsource responsibility, but you can outsource complexity. Start with the checklist, review every layer, and make sure your site is not just fast—but safe.
WordPress powers a massive part of the internet for a reason. With the right moves, it doesn’t have to be a liability. It can be a secure, stable foundation for your business or your clients.
Secure it properly. Run it consistently. And never treat security like a “set it and forget it” feature again.

